You are here
A Step Beyond Sabre Rattling: Notes from the Ukraine–Russia Cyberconflict
Cyberattacks are not new to Ukraine. They have been part and parcel of its conflict with Russia from the first crisis in 2017, with the ebb and flow of such attacks in sync with escalation in the border conflict. The current crisis has been no different with the initiation of the crisis itself being marked by an escalation in the intensity of these attacks. They have largely taken the form of distributed denial of service (DDoS) attacks which are designed to take critical websites offline through a virtual cyber bombardment as well as implanting malware disguised as ransomware on sites and taking them offline (See Fig. 1).
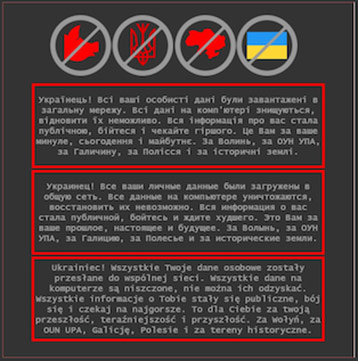
Source: Bill Toulas, “Multiple Ukrainian Government Websites Hacked and Defaced”, BleepingComputer.com, 14 January 2022.
The first ransomware attacks using a hitherto unknown malware, WhisperGate, was reported on 14 January 2022 and has continued ever since, with the most recent attacks having taken the websites of the Ministry of Defence and two banks offline.1 Australia, along with the United Kingdom and the United States publicly attributed these attacks to the Russian Main Intelligence Directorate (GRU).2 For its part, Russia has consistently denied that cyberattack has emanated from its territory.3
Agencies in other countries that are involved in the conflict like the United States (US) have also issued advisories to the effect that cyberattacks may be expected whether or not the conflict escalates. The international community and cybersecurity professionals, in particular, would have unpleasant memories about the last time conflict escalation took place in Ukraine with concomitant cyberattacks using the NotPetya malware which, though targeted at Ukrainian entities, subsequently escaped into the wild and resulted in a cumulative loss of US$ 14 billion to governments and businesses worldwide. Thus, this is an issue that concerns not just the immediate parties affected, but the international community as a whole.
The first reports of cyberattacks in Ukraine appeared on 14 January and this took the form of website defacements of government agencies and the destruction of data using wiper software. Called WhisperGate by Microsoft researchers, the malware bore resemblance to the NotPetya malware used in the 2017 cyberattacks on Ukraine, but “with added functionalities”. These additional functionalities were added to overcome any new protections that had been built into systems following the earlier attacks. According to CISCO security researchers, the attackers were advanced persistent threat (APT) actors, probably present for months or years in these systems which they would have accessed through credentials obtained through spear-phishing.4 Like the NotPetya malware, WhisperGate also masquerades as ransomware, with a fake ransom note warning that the user’s hard drive had been corrupted and would be restored only on payment of US$ 10,000 via bitcoin.
Depending on whether the crisis escalates or tapers down, this is only the first salvo in a scenario where subsequent attacks could be carried out on critical services such as electricity, transportation, finance, and telecommunications. The North Atlantic Treaty Organization (NATO), the security treaty organisation at the centre of Russia’s disenchantment with Ukraine, signed an agreement in January to deepen technical and military cyber cooperation, “including Ukrainian access to NATO’s malware information sharing platform”.5 Ukraine was subjected to more than 2,88,000 cyberattacks in the first 10 months of 2021.6 While almost all countries are subjected to cyberattacks, these are of a completely different magnitude comprising both attacks on critical infrastructure as well as disinformation campaigns designed to reduce the trust of the general population in these systems and the government.
With the US and European countries threatening sanctions against Russia, there is a justified concern that these attacks would be directed against those countries as well. Many countries, including Poland, Lithuania, the UK, and the US have issued advisories. A detailed advisory jointly brought out by the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and National Security Agency (NSA) on 11 January detailed the steps various organisations could take to heighten their security posture and protect their critical assets.7 Organisations were also urged to lower their thresholds for reporting suspicious cyber activity to government agencies in subsequent advisories. The White House, while downplaying the possibility of imminent cyber strikes on the US, said: “We have a range of tools at our disposal to use and react–in reaction, and the President reserves the right to do that”.8 In a similar vein, the UK also warned Russia that it was prepared to make retaliatory cyberattacks if British computer networks were threatened.9
Unlike the attacks of 2017 which spread havoc worldwide, the perpetrators this time around have learnt from 2017 and ensured that they remain localised to Ukraine.10 Cybersecurity providers and software companies are also seemingly ahead of the problem and putting out advisories and issuing patches at a faster rate. Cyberattacks in this conflict, in a sense, has become normalised in that they are more focused, there is no lasting damage, and it only serves to convey a sense of impotence and helplessness to the affected government and population. At the same time, it also signals to other governments that they are also not impervious to such attacks. As noted by a senior American politician recently, the US does not have the luxury of two oceans serving as natural barriers in cyberspace and will have to take the cyberthreat seriously. However, the US does have the heft to deter more severe attacks by virtue of its own capabilities, and to sanction and prosecute individuals identified as perpetrators of less severe attacks, as it has done, in a number of cases.11 This, though, does not seem to have had much effect on containing low-level cyberattacks and intrusions.
Ironically enough, Russia has been at the forefront of multilateral processes at the United Nations to secure cyberspace, including, sponsoring the resolution that led to the establishment of the Open-Ended Working Group (OEWG) on the security of and in the use of information and communications technologies in 2018, further renewed till 2025. The main agenda of this group is to “further develop the rules, norms and principles of responsible behaviour of States”.12 The events of the past month show that this will be a long time coming. It would not be out of place here to mention that like the Petya malware of 2016, and the NotPetya and WannaCry malware attacks in May 2017, WhisperGate also contains traces of the EternalBlue exploit which was obtained by hackers from the US NSA’s cyber toolkits.
The fact of the matter is that while countries are publicly professing the goal of stable cyberspace, there is frenetic activity going on behind-the-scenes to ramp up offensive capabilities, the severity of which can be adjusted according to need. The fact that the issue of cyberattacks continues to be in a grey zone from the perspectives of the perpetrator, the victim, and the bystander emboldens the former to continue with these attacks unabated. The sooner one faces up to the changing realities and adjusts policies and capabilities accordingly, the better it would be.
Views expressed are of the author and do not necessarily reflect the views of the Manohar Parrrikar IDSA or of the Government of India.
- 1. “Ukraine Defence Ministry Website, Banks, Knocked Offline”, Reuters, 16 February 2022.
- 2. “Attribution to Russia of Malicious Cyber Activity against Ukraine”, Ministry of Foreign Affairs, Australia, 20 February 2022.
- 3. “Russia Rejects Claims It Was Responsible for Cyberattack on Ukraine”, Reuters, 19 February 2022.
- 4. Charlie Osborne, “Researchers Break Down WhisperGate Wiper Malware Used in Ukraine Website Defacement”, ZDNet, 24 January 2022.
- 5. “Statement by the NATO Secretary General on Cyber Attacks Against Ukraine”, NATO, 14 January 2022.
- 6. Luke Harding, “Ukraine Hit by ‘Massive’ Cyber-attack on Government Websites”, The Guardian, 14 January 2022.
- 7. “Understanding and Mitigating Russian State-Sponsored Cyber Threats to U.S. Critical Infrastructure”, Cybersecurity and Infrastructure Security Agency (CISA), 11 January 2022.
- 8. “Press Briefing by Press Secretary Jen Psaki, January 26, 2022”, The White House, 26 January 2022.
- 9. Rob Merrick, “Ukraine: UK Ready to Launch Retaliatory Cyber-attacks on Russia, Defence Secretary Tells MPs”, The Independent, 21 February 2022.
- 10. “WhisperGate: Not NotPetya”, Secureworks Counter Threat Unit Research Team, 21 January 2022.
- 11. “US Imposes Sanctions on Russia Over Cyber-attacks”, BBC News, 16 April 2021.
- 12. “First Committee Approves 27 Texts, Including 2 Proposing New Groups to Develop Rules for States on Responsible Cyberspace Conduct”, United Nations General Assembly, GA/DIS/3619, 8 November 2018.